Over 200,000 messages from Black Basta, a notorious ransomware syndicate operating since 2022 and as a ransomware-as-a-service (RaaS), have been exposed by a member in retaliation to how the syndicate targeted Russian banks. These messages, spanning through a year, contain tactics and secrets the syndicate used in carrying out their ransomware operations.
In November 2024, the Federal Bureau of Investigation (FBI), Cybersecurity and Infrastructure Security Agency (CISA), Department of Health and Human Services (HHS), and the Multi-state Information Sharing and Analysis Center (MS-ISAC) in a joint Cybersecurity Advisory (CSA), announced the activities of Black Basta and called the group “a ransomware variant whose actors have encrypted and stolen data from at least 12 out of 16 critical infrastructure sectors, including the Healthcare and Public Health (HPH) Sector.”
“Black Basta is considered a ransomware-as-a-service (RaaS) variant and was first identified in April 2022,” says the advisory. “Black Basta affiliates have impacted a wide range of businesses and critical infrastructure in North America, Europe, and Australia. As of May 2024, Black Basta affiliates have impacted over 500 organizations globally.”
Ascension Health, one of the leading non-profit providers of health services in the US was a victim of one of Black basta’s cyberattacks during this period.
Thomas Roccia, a Senior Threat Researcher at Microsoft, using python and generative AI to work independently through the leaked data made a post on X (fka Twitter) to share his findings: His analysis shows that Black Basta runs a highly professional Ransomware-as-a-service operation where the group develops and maintains its ransomware tool, as well as rigorously vets affiliates to carry out the attacks.
The chats, according to his analysis, revealed a dual extortion tactic – where victims risk both their data (sensitive information) being encrypted and the threat of the release of said data if ransom is not paid. Roccia also found a structured revenue-sharing model where payment is split between the developers and the affiliates.
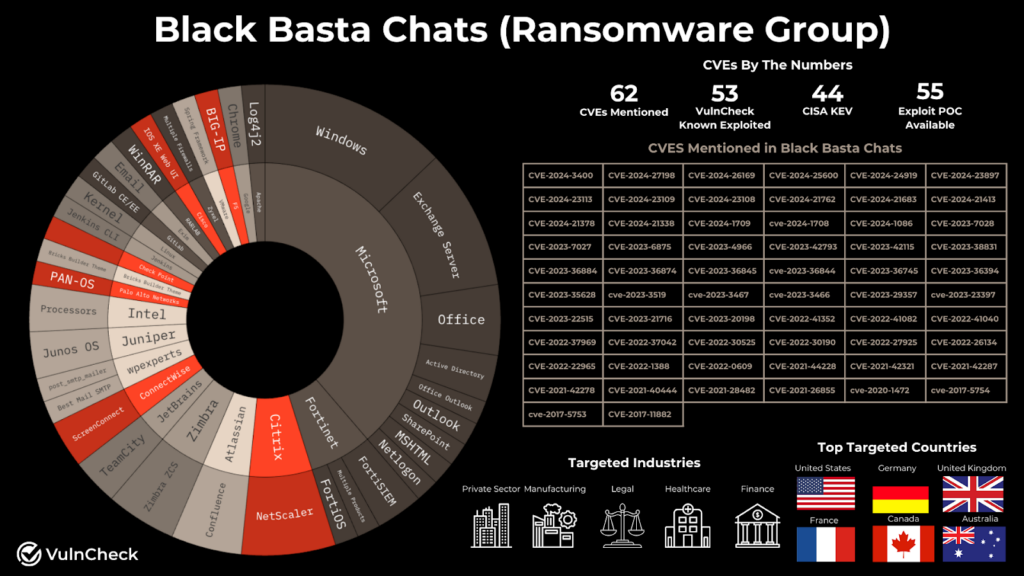
Patrick Garrity, in his research, also explains that the group references 62 distinct vulnerabilities – 50 of which are known to have been exploited, with 44 flagged in CISA’s Known Vulnerabilities list. The leaked chats show Black Basta’s focusing on widely used platforms like Windows, Office, and NetScaler, and prioritizing those with available proof-of-concept exploits.
This approach gives them a clear course to then infiltrate organizations in sectors such as healthcare, finance, and manufacturing.
Important to note that the Russian-populated group is reported to have been paid over $100 million for ransomware by their victims, according to a research done by Elliptic in November 2023.
Right from the inception of Black Basta in 2022, researchers hinted that it might be an offshoot of Conti, a notorious ransomware group that was widely known for its particularly large-scale attacks on critical infrastructure sectors in healthcare. It also suffered the same fate as Black Basta, where leaked internal communications and the activities of law enforcement agencies forced the group to disband in early 2022.
However, while Black Basta immediately seized their operations since the group’s data was leaked, Cybersecurity researchers are taking it upon themselves to continue analyzing the leaked logs in order to gain better insights into potential future threats.

