In March 2026, authorities around the world announced a major success in cybersecurity after they shut down a 3 million device botnet. This criminal network took over millions of devices connected to the internet.
Because these devices were controlled by criminals, they could be used to attack websites, slow down services, and cause problems for businesses and individuals.
To stop this, law enforcement agencies in the United States, Germany, and Canada worked closely with cybersecurity companies. As a result, the attackers lost control of the devices and could no longer carry out their attacks.
How the Botnet Worked
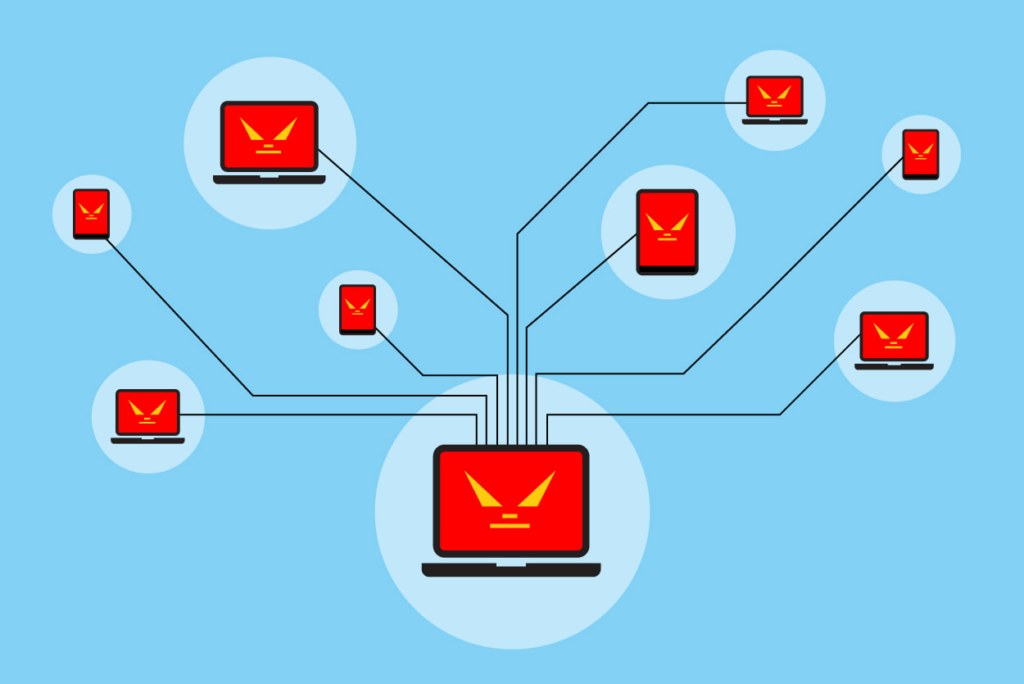
To understand the significance of what happened, it is important to know how these botnets worked. First, attackers scanned the internet for devices with weak passwords or outdated software.
Once they found a vulnerable device, they installed malware and secretly took control of it. Then, the infected device became part of a larger network controlled by the criminals.
After enough devices were infected, attackers sent instructions to all of them at the same time. The devices then flooded targeted websites with massive amounts of traffic. Because millions of devices acted together, the attacks became extremely powerful.
Also, some attacks reached more than thirty terabits per second, which overwhelmed servers and caused online services to go offline. As a result, businesses and users experienced slowdowns and outages.
What Happened in the 3 Million Device Botnet Takedown
First, investigators found the main structure of four big botnets called Aisuru, Kimwolf, JackSkid, and Mossad. After identifying which devices were infected, authorities quickly took control of the domains and servers the criminals used.
At the same time, cybersecurity experts studied the network traffic from the botnets to understand how widespread the problem was. Because of these actions, millions of devices were removed from the network and the attackers could not continue their operations.
Why the Botnet Takedown Matters
This incident matters greatly because it removed a massive attack network from the hands of criminals.
However, it also showed how vulnerable our everyday devices are. Many routers, cameras, and smart devices still use weak passwords or outdated software. Therefore, attackers could exploit these weaknesses to build new botnets in the future.
In addition, the scale of this botnet shows how quickly cyber threats can grow. When millions of devices are compromised, attackers can disrupt major online services. Because of this, both individuals and organizations face increasing cybersecurity risks.
Could Your Devices Be Affected
Even though authorities shut down these threats, many devices still remain at risk. A smart TV, router, or home security camera can become infected without obvious signs. Sometimes users notice slower performance or unusual internet activity but many infected devices hardly show any changes.
Because of this, users should assume that any unsecured device could be vulnerable. At the same time, organizations should monitor their networks for unusual activity. By taking these precautions, users can reduce the chance that their devices join another botnet.
How to Protect Yourself Going Forward
To reduce the risk, users should replace default passwords with strong credentials. They should also enable automatic updates so devices receive security fixes promptly.
In addition, connect smart devices like TVs and cameras to a different WiFi network if possible. This way, if one device gets hacked, attackers cannot easily access your phone or laptop. You should also watch for unusual internet activity, such as slow speeds or unknown devices connected to your WiFi.
However, attackers will never stop searching for vulnerable devices so this botnet takedown is definitely not a permanent solution. Ultimately, the ball is in the user’s court and they must take all necessary measures to protect their devices to prevent cases like this in the future.

